Mar 5, 2026

By Ammar Khan
Marty Weiner wants you to understand that spam has nothing to do with breaking into a vault. He’d liken it more to spray paint. "With security, you're building big walls so there's just no chance," he says. "With spam, they're spray painting on the outside while you try to put up special material that makes their spray paint not work."
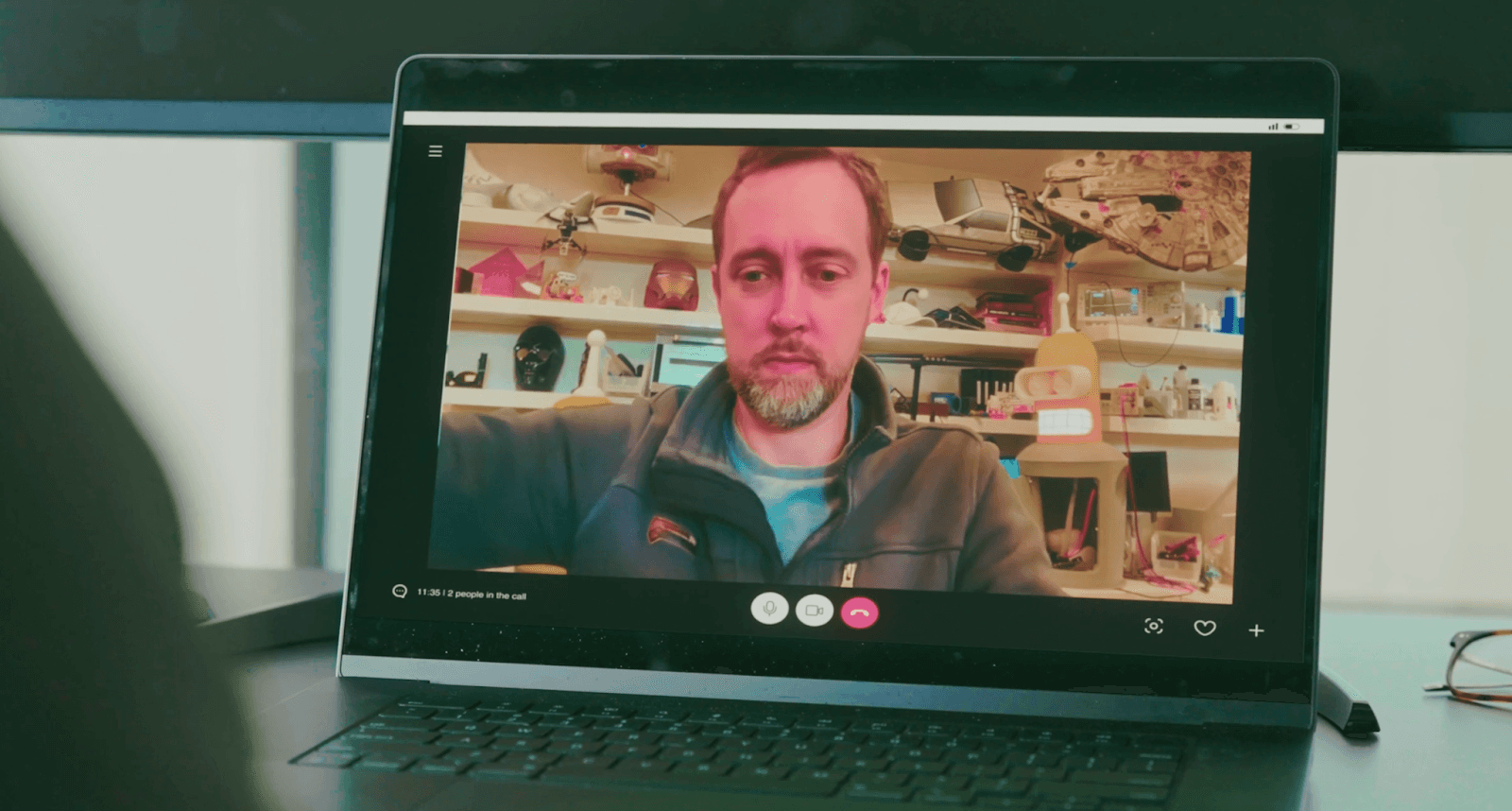
This is how Marty talks, and it's very fun to listen to (just ask his dev team). He has the gift of gab, which makes sense when you consider he's spent the better part of fifteen years explaining absurdly complicated systems to people who need to act on them fast. As one of the founding engineers at Pinterest and the former CTO of Reddit, Marty has been in the room for some of the biggest trust and safety challenges the consumer internet has produced. He's also the CTO and co-founder of VerifyYou, which means he's now building the thing he spent a decade wishing existed.
I sat down with Marty to talk about what he learned fighting spam across two platforms, how the game has changed with AI, and why he thinks the internet is eventually going to have to make a trade-off that most people haven't reckoned with yet.
* * *
The Pinterest Years: Lightning, Luxury Scams, and a 100,000-Node Botnet
Marty joined the company that became Pinterest before Pinterest was Pinterest. "I joined before it even had its current name," he says, laughing. "There was no spam yet." The product launched, puttered along for about nine months, and then, as he describes it, "seemed like overnight it started shooting up."
The first inklings of spam appeared around early 2012. A Pinterest clone, likely operating out of Germany, was trying to steal traffic and gain a European foothold by selling users downstream. Then the targeted campaigns followed. Pinterest's core demographic at the time was women between 25 and 45, and the spammers figured this out fast. "I learned a lot about women's fashion during this time," Marty says. The spam took the shape of fake discounts and free gift cards for luxury items, all designed to funnel people to external sites where the money was made through scams, product sales, credential theft, or some combination of all three.
Because Pinterest was such a high-value target, the attacks scaled fast. One campaign used a botnet of over 100,000 nodes distributed across the world. Marty built a team of ten engineers and six operations people to fight it. They got so good, he says, that "we had to shift our metrics several times just to find more spam to stop."
And then he drops what might be my favorite detail from the entire conversation: "One of my favorite observations was that spammers' pins were getting something like ten times more views per unit time than organic content. Their success as essentially professional marketers was what took them down."
The spam worked so well that it looked anomalous. The attackers were too good at their own game, and that's what made them visible.
* * *
Rational Actors, Irrational Actors, and Why the Difference Changes Everything
When Marty talks about defense strategy, he keeps coming back to a distinction that he clearly thinks about a lot: rational actors versus irrational actors.
"The reason the rational actor thing is so effective is there's a feedback loop, and we can exploit that feedback loop in many, many ways," he explains. Most spammers are rational. They have costs, revenue targets, an economic model. They're running a business, basically. And if you can squeeze that business hard enough, if you can make the cost of attacking higher than the revenue it generates, they go away. At Pinterest, Marty's team studied adversarial strategic models, including OODA loops, to systematically squeeze the economics of spam until it stopped making sense.
Irrational actors are a different animal entirely. "The irrational actors are like the state actors," Marty says. "Somebody from Russia, attacking and not really having a bank account to worry about. They have essentially infinite money." For those, the strategy starts to break down because there's no economic feedback loop to exploit. You can use similar tactics, but the fundamental leverage is gone.
This distinction sounds academic until you realize most T&S teams treat every threat the same way. They build one set of tools and point them at everything. Marty's argument is that this is a structural mistake. Rational actors and irrational actors require fundamentally different playbooks, and conflating them means you're doing both jobs badly.
* * *
The Friction Paradox (Or: How Pinterest Made Spam Inevitable)
There's a tension at the heart of every consumer platform that Marty describes with the precision of someone who lived inside it for years: friction is the enemy of growth. Pinterest kept reducing signup barriers, and every barrier they removed was a signal Marty's team lost.
"When we began, you had to have a Twitter or Facebook account, a password, and we put you through a bunch of other stuff," he says. "By the end, it was like, you're in. Let's pick a username. Oh, we picked one for you. Password? Nah, don't worry about it." He pauses. "That means there's just zero signal to go off of."
This is the paradox: Pinterest was right to reduce friction. That's how you grow. But every piece of friction you remove is a piece of signal you lose, and signal is what lets you tell humans from bots. The platform was making the rational growth decision while simultaneously making Marty's job harder. And he doesn't blame them for it. "Rightfully so," he says about the friction reduction, multiple times. He gets it. He just had to build around it.
Their answer was a layered approach. Machine learning scraped off the bottom 60% of low-effort attacks, the obvious garbage. But the real work was done by a small, well-tooled operations team that could find and nuke hundreds of thousands of pieces of spam in minutes. The key insight: the ops team was more effective than the ML, because the sophisticated attackers who got past automated defenses required human pattern recognition and human judgment.
* * *
The Internet Was Built Without Trust (And Now We're Paying For It)
This is where the conversation shifts from looking backward to looking forward, and where you can feel Marty thinking through something he hasn't fully resolved yet.
"The internet, actually, in the beginning, had trust," he says. "We're talking DARPA net, 1969. It was a network of computers in the Department of Defense and universities. If someone was misbehaving, I know who they are. I can literally go slap them on the back of the head." He points out that .edu domains still carry a kind of inherited trust for this reason. "If that email gets abused, it goes right back to the school, and someone's getting kicked out."
But the open internet was never built with that trust layer. "You could pretend to be Warren Buffett and send an email from warren.b@berkshirehathaway.com," Marty says. "Easily. There's just no trust built into the base layer." Combine that with platforms that want zero friction, users who want anonymity, and AI that's making attacks cheaper and more convincing by the month, and you get what Marty sees as an inevitability: "It's only getting worse. AI is leveraging up the attackers. To me, it's a matter of time before it all breaks."
His answer, and the reason he co-founded VerifyYou, is what he calls an "air gap." If you can put space between the platform and the verification, if the company never touches the sensitive data but can still confirm a user is human, you preserve anonymity while introducing trust. "If we can make an air gap where the companies don't get this information, the anonymity is maintained, and we can play the game of collecting whatever we need to reduce bad behavior, then I think that's the way the internet is going to have to go."
* * *
Prevention, Mitigation, Recovery
If there's a single framework Marty wants people to take away, it's this: think about defense in three phases, not one.
Prevention means making attacks not worth attempting. He calls it "skin in the game." Monetary cost, social reputation, legal risk, the perception of consequences. Layer enough of these and rational actors walk away before they start. Mitigation is what most teams already do: catching bad stuff after it gets in. Behavioral signals, ML models, human ops teams. Recovery is the phase most teams forget entirely: the game doesn't end when an attack succeeds. "Suppose it's ticket sales," he says. "The concert's in a month. It takes some time for that ticket to be resold. If within an hour, we can feed information back and say, hey, this was fraudulent, they can remove it, and we still win."
The argument is that most teams over-invest in mitigation and under-invest in everything else. Prevention can stop attacks before they start. Recovery can reverse damage after they succeed. Together, they change the economics of the entire game.
* * *
Talking to Marty about spam is like hearing a grizzled general reminiscing on past battles and a war that is long from over. The tactics have changed completely since 2012, but the strategy, the way he thinks about the problem, hasn't. "As long as we're fighting rational actors," he says, "I don't think there's any reason the strategy would change. It's just wholly different tactics."
The internet has a trust problem that was baked in from the beginning, and it's getting worse faster than most people realize. Marty has spent more than a decade learning, sometimes painfully, what works and what doesn't. And now he's building the thing he kept wishing he had.
Marty Weiner is the CTO and co-founder of VerifyYou. He was the former CTO of Reddit and a founding engineer at Pinterest.